XML Vulnerabilities And Security Risks
There are a number risks associated with XML, ranging from poor design and coding practices to intentional exploits
that pose poential security threats. Here are some of the most common XML related vulnerabilities.
XML Bomb
This involves a large number of references to a named entity, which, upon expansion, can result in exhaustion of memory.
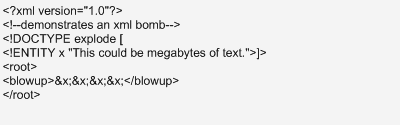
If the definition of explode is large and there is also a large number of references to it, memory could be depleted upon expansion of the entity. As recently as this year, the vulnerability of such XML bombs exists in XML parsers from major vendors. Its history, complete with references, is provided in this article: http://soa.sys-con.com/node/1092377
Access To An Externally Referenced File
If the XML contains a Document Type Definition (DTD), a file containing sensitive data, possibly in a remote location, may be referenced in an entity declaration. If the XML document is opened and read by a software program, particularly one that uses an XML parser, the program may attempt to open and read the sensitive file. It is not uncommon for XML files to be received by persons who are unaware that such a file is referenced within the XML document. Or the file may be submitted to an automated process without such awareness.
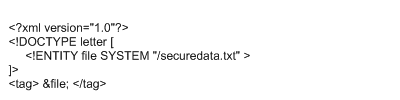
If the securedata.txt file is located on a remote server, as in "http://company.com/securedata.txt" two additional
vulnerabilites may exist. First, the server may be owned by a malicious entity and just accessing it could result
in infection by malware, spyware, viruses or trojans. Second, if the file being accessed is very large, many
gigabytes for example, that could result in a denial-of-service.
See
Http Overload on how to block access to such files.
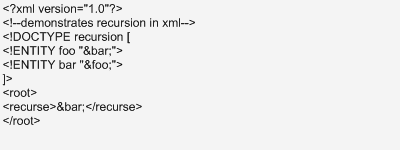
Entity Recursion
This is basically recursive expansion of named entities that can result in consumption of huge amounts of memory,
possiblly leading to denial-of-service, as in the following example:
Submitted by Bill Conniff, Founder of Xponent, on February 20, 2010